COVID-19 Easy Fix Remote Work Cyber Security Checklist
Direct answer: A practical way to reduce COVID-19 remote-work cyber risk is to run a role-based checklist for management, employees, and directors that covers communication, endpoint control, access policy, and phishing readiness.
The earlier article 'Coronavirus (COVID-19) Guidance for Small and Large Businesses' listed resources and planning points for emergency response. With large-scale work-from-home adoption, threat actors increased malicious email and social engineering attempts.
This checklist was designed to help organizations quickly understand whether key remote-work risk factors are being addressed and where management focus is needed.
The checklist is divided into three parts based on roles and responsibilities across the organization.
What should senior management review in remote-work cybersecurity?
| # | Questions | Yes | No |
| 1 | Is the CEO present in online tools, channels, and is communicating proactively and engaging in timely conversations? | ||
| 2 | Has the management explained in writing what the company is trying to accomplish and has a vision that can help employees rally behind? | ||
| 3 | Has management addressed the issues raised by employees? | ||
| 4 | Is management courteous, compassionate, and authentic across channels? | ||
| 5 | Does the company have online expressions for your culture? The virtual water cooler where high fives, celebrations, gossip, community, family, personal interest, happy emojis, etc. can be shared. | ||
| 6 | Does the company have the right digital tools to facilitate communication? (E.g., Text messaging, Slack, email, wikis, hangout, video conferences, etc.) | ||
| 7 | Do the company have established security policies and guidelines for remote work? |
What should employees review in remote-work cybersecurity?
| # | Questions | Yes | No |
| 1 | Is your Wi-Fi connection secure? Can you reach out to the support team to verify and test? | ||
| 2 | Is anti-virus or any updates/patches applied timely to the computer without delay? | ||
| 3 | Do you back-up periodically in addition to auto backup runs? | ||
| 4 | Do you lock your screen while away and protect them from kids? | ||
| 5 | Did you check with your support team that encryption is in place and working? | ||
| 6 | Are you familiar with applicable security guidelines, plans, and policies? | ||
| 7 | Are you aware that the work computer and other devices must not be shared? |
What should directors review in remote-work cybersecurity?
| # | Questions | Yes | No |
| 1 | Do you have adequate support staff to address the questions from remote workers and resolve the issues in time? | ||
| 2 | Do you have the ability to push updates, patches, etc. and enforce timely implementation? | ||
| 3 | Can you provide virtual solutions, digital signature, and approval workflows? | ||
| 4 | Do you have clear procedures for employees to follow in case of a security incident? | ||
| 5 | Can you limit access to sensitive data where it makes sense? | ||
| 6 | Do you have a data breach and incident response plan to manage incidents? | ||
| 7 | Did you send a reminder to employees as to what information needs to be protected? (E.g., confidential, sensitive business information, trade secrets, intellectual property, private employee information, work product, customer information, and other personal information that identifies a person.) | ||
| 8 | Have you trained employees on how to detect and/or handle phishing attacks and other forms of social engineering attacks? | ||
| 9 | Do you have a policy in place to prohibit access to company information systems while on public wi-fi? | ||
| 10 | Do you have solutions in place to manage and secure mobile devices and applications? | ||
| 11 | Are you communicating with employees about coronavirus-themed phishing emails? |
What supporting guidance and phishing example are included?
The checklist references guidance and articles from Fast Company, ENISA, JDSPURA, BBC, CNBC, and other related sources.
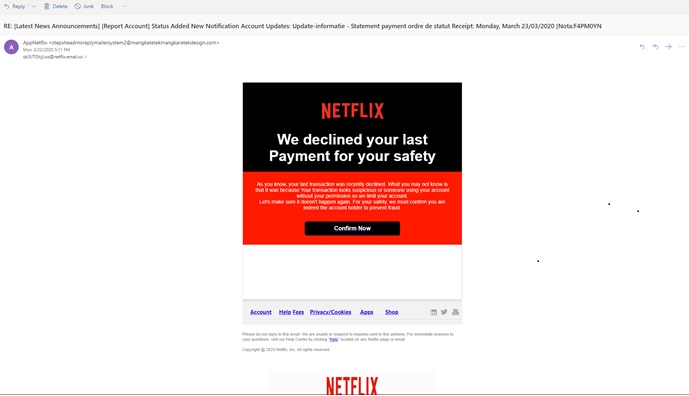
The post also shares a phishing email example to support awareness training.
Key Takeaways
- Use role-based accountability to execute remote-work controls consistently.
- Prioritize secure home connectivity, patching, backups, encryption checks, and device handling.
- Maintain clear incident reporting and response pathways for remote employees.
- Continuously train teams on coronavirus-themed phishing and social engineering patterns.
Related Resources
Related Posts

COVID 19, Remote Work, and Cyber Security
A role-based remote-work cybersecurity checklist for management, employees, and directors, covering phishing awareness and incident response readiness.
Read More
COVID-19 Quick Remote Work Cyber Security Checklist
Use a practical role-based checklist to validate remote-work controls, communication discipline, and endpoint security expectations.
Read More
Senior Mgt & Employee Responsibilities - COVID 19
Define management and employee responsibilities clearly to reduce remote-work security gaps during rapid operating-model changes.
Read More

GRC Insights That Matter
Exclusive updates on governance, risk, compliance, privacy, and audits — straight from industry experts.