Prevention, Detection and Recovery from Cyberattacks
Direct answer: Organizations improve cyber resilience by understanding who attacks them, which attack paths are most likely, and by enforcing basic security controls such as patching, strong authentication, and phishing resistance.
Many organizations still rely on ad-hoc or outdated incident response practices, even as remote work models, cloud expansion, and evolving threat techniques increase operational risk.
This article focuses on practical threat actor awareness and baseline controls that materially improve prevention, detection, and recovery outcomes.
Who are the main threat actors and why does it matter?
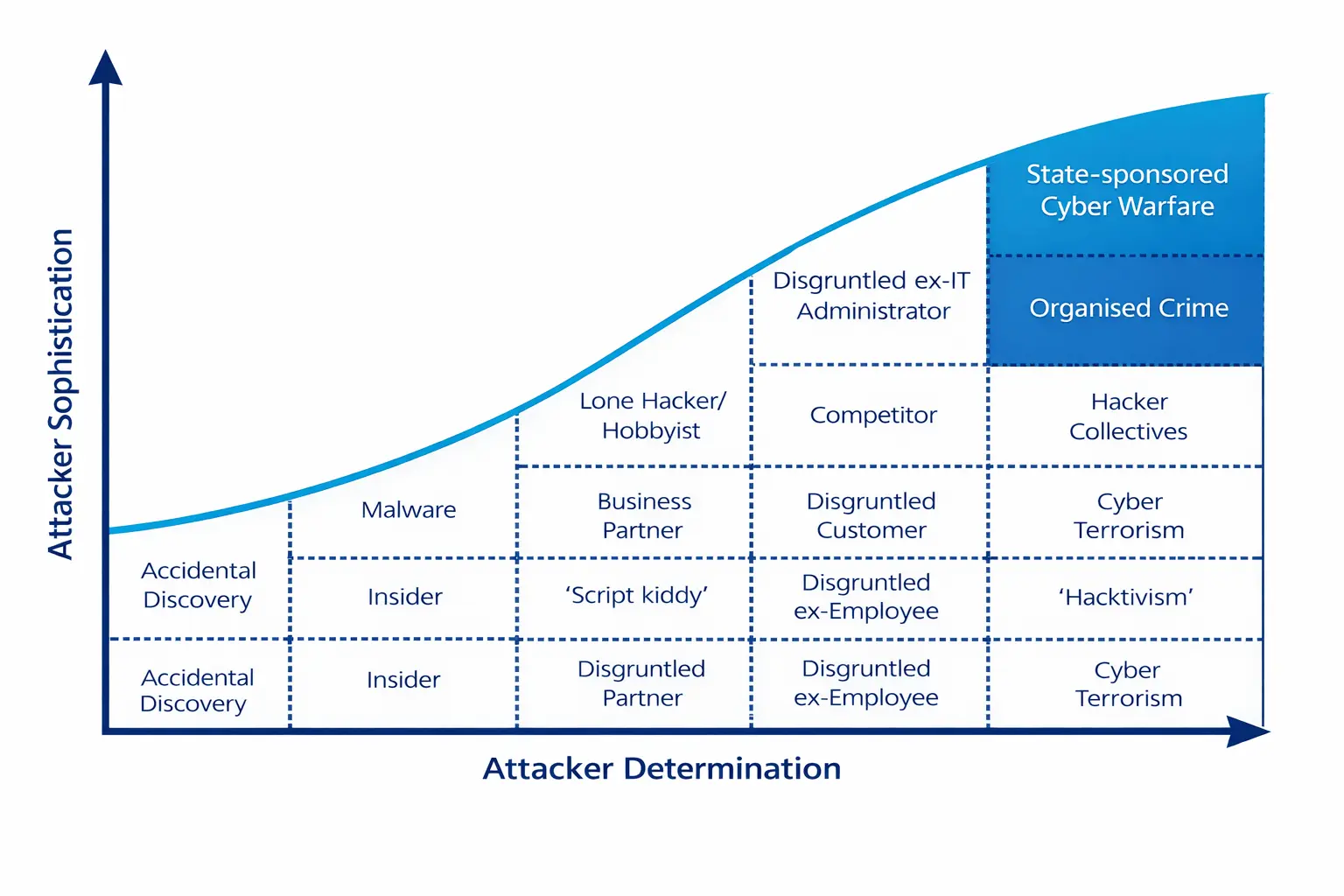
Cyber defense decisions improve when security teams understand attacker capability and determination. Threat actor profiling helps prioritize controls, tune detections, and improve response playbooks.
As threat tactics evolve, organizations should continuously adapt prevention and recovery approaches rather than relying on static yearly plans.
What are typical sources of cyberattacks?
Common external and internal attacker sources include:
- Organized crime groups
- State-sponsored or geopolitically aligned actors
- Independent hackers and brokered-access groups
- Competitors or industrial espionage actors
- Insiders such as disgruntled employees or contractors
Insider risk remains significant because legitimate access can be abused without strong monitoring and least-privilege controls.
Which basic security gaps are most commonly exploited?
Attackers frequently succeed through preventable control failures and routine operational gaps:
- Weak or reused passwords and missing MFA
- Default credentials on infrastructure or applications
- Delayed patching and outdated endpoint protections
- Unsafe use of public or untrusted networks
- Phishing and social engineering that bypass user vigilance
Basic hygiene closes a large percentage of initial access opportunities and improves downstream recovery performance.
FAQ: How often should incident response plans be tested?
Run tabletop exercises at least quarterly and perform broader technical simulations at least annually, plus after major infrastructure, vendor, or process changes.
FAQ: What is the fastest way to improve cyber resilience?
Start with MFA enforcement, patch prioritization for internet-facing assets, phishing drills, endpoint visibility, and a validated incident escalation workflow.
FAQ: Should small teams invest in detection or prevention first?
Both matter, but prevention basics should be stabilized first, then detection and response depth should be expanded based on asset criticality and threat exposure.
Key Takeaways
- Threat actor awareness improves prioritization and control design.
- External and insider threats both require continuous monitoring.
- Most successful attacks still exploit basic hygiene failures.
- Frequent plan testing and operational drills improve recovery confidence.
Related Resources
Related Posts
Prevention, Detection, and Recovery from Cyberattacks- Part I
A Monday morning cybersecurity reality check: why human error matters, and a practical list of cyberattack myths vs realities every organization should know.
Read More
Prevention, Detection, and Recovery from Cyberattacks - Part II
Review your incident response readiness with a practical checklist covering six IR phases, audit questions, and standards mapping for prevention, detection, and recovery.
Read More
Prevention, Detection, and Recovery from Cyberattacks Part III
Is Zero Trust a model for effective and efficient security? This guide explains what Zero Trust is, the technologies that support it, and what organizations are doing to adopt it.
Read More

GRC Insights That Matter
Exclusive updates on governance, risk, compliance, privacy, and audits — straight from industry experts.