Many organizations have already started preparing for the Digital Personal Data Protection (DPDP) Act. Some have completed privacy assessments, while others are still identifying compliance gaps. However, the biggest challenge is not understanding the requirements - it is executing them in a structured and measurable way.
A DPDP compliance roadmap helps organizations move from scattered compliance activities to a coordinated program that aligns legal, privacy, security, IT, operations, and leadership teams.
This article explains the complete DPDP implementation roadmap, including governance, data discovery, consent management, Data Principal rights, vendor oversight, security controls, breach response, and audit readiness. It also includes a practical 90-day execution model that organizations can use to accelerate compliance.
What Is a DPDP Compliance Roadmap?
A DPDP compliance roadmap is a structured implementation plan that helps organizations identify, manage, protect, and govern personal data throughout its lifecycle.
It provides a clear sequence of activities, ownership responsibilities, timelines, controls, and evidence requirements needed to demonstrate compliance.
A strong roadmap helps organizations answer critical questions:
- What personal data do we collect?
- Why do we process it?
- Where is it stored?
- Who has access to it?
- Which vendors process it?
- How do we prove compliance during audits?
Unlike a checklist, a roadmap focuses on execution and continuous improvement.
A DPDP compliance roadmap is a step-by-step plan that helps organizations implement privacy controls, manage personal data responsibly, and demonstrate compliance with the Digital Personal Data Protection Act.
Why Organizations Need a DPDP Implementation Roadmap
Many organizations struggle because privacy activities are distributed across multiple teams.
- Legal teams manage notices and contracts.
- IT teams manage infrastructure.
- Security teams manage safeguards.
- Operations teams handle business processes.
Without a unified roadmap, compliance efforts often become fragmented.
A roadmap creates alignment by establishing:
- Governance structures
- Clear ownership
- Compliance milestones
- Accountability mechanisms
- Continuous monitoring
This reduces delays, duplication of effort, and compliance risks.
Key Workstreams in a DPDP Compliance Roadmap
A successful implementation program should include the following workstreams:
1. Governance and Ownership
Organizations should establish accountability for DPDP compliance across departments.
Key activities include:
- Defining compliance ownership
- Assigning executive sponsors
- Creating escalation procedures
- Establishing reporting structures
Related Resource: Data Fiduciary Under DPDP Act
2. Personal Data Discovery
Organizations cannot protect personal data they cannot locate.
The first operational step is identifying where personal data exists across systems, applications, cloud platforms, endpoints, shared drives, and third-party tools.
Key activities:
- Structured data discovery
- Unstructured data discovery
- Shadow data identification
- Data classification
Related Resource: DPDP Data Discovery Compliance Guide
3. Data Inventory and Mapping
Once data is discovered, organizations should create a centralized inventory.
A data inventory should capture:
- Data categories
- Processing purposes
- System owners
- Storage locations
- Vendor access
- Retention periods
- Security controls
Data mapping should then show how information moves across systems and business processes.
Related Resources:
4. Consent Management
Organizations must implement processes to collect, record, manage, and withdraw consent.
A mature consent framework includes:
- Consent collection
- Consent history
- Preference management
- Withdrawal handling
- Evidence retention
Related Resource: Consent Management Platform
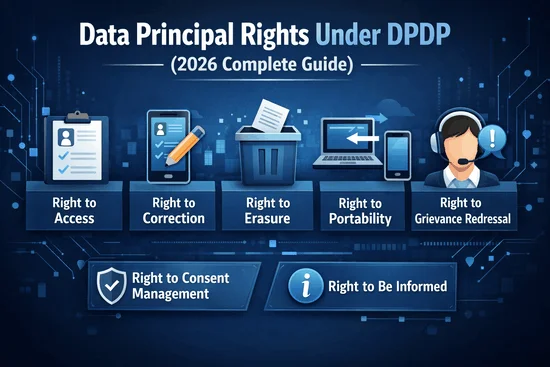
5. Data Principal Rights Management
Organizations must establish workflows for handling requests related to:
- Access
- Correction
- Erasure
- Consent withdrawal
- Grievance redressal
- Nomination
An effective process includes identity verification, assignment workflows, SLA tracking, approvals, and evidence storage.
6. Vendor and Processor Risk Management
Many compliance failures originate from third parties.
Organizations should evaluate:
- Vendor access to personal data
- Security safeguards
- Breach notification obligations
- Contractual commitments
- Data deletion practices
Related Resource: Vendor Risk Management Under DPDP
7. Security Controls
Privacy and security must work together.
Key controls include:
- Access management
- Encryption
- Logging and monitoring
- Vulnerability management
- Backup controls
- Secure deletion
Related Resource: DPDP Data Security Controls
8. Breach Response and Incident Management
Organizations should establish documented workflows before an incident occurs.
A breach response program should include:
- Detection procedures
- Escalation processes
- Investigation workflows
- Notification requirements
- Evidence collection
Related Resource: DPDP Data Breach Notification Workflow
9. Audit Readiness and Evidence Management
Compliance cannot be demonstrated without evidence.
Organizations should maintain:
- Consent records
- Data inventories
- Vendor assessments
- Risk assessments
- Incident logs
- Policy approvals
- Training records
The 90-Day DPDP Execution Roadmap
Many organizations attempt to implement everything simultaneously and lose momentum.
A phased 90-day execution model helps teams prioritize high-risk activities first.
Days 1–30: Fix Critical Risk Gaps
The first phase should focus on issues that create immediate regulatory or operational exposure.
Priority Activities
- Identify critical personal data systems
- Build consent workflows
- Define breach escalation procedures
- Assign ownership
- Review high-risk vendors
Deliverables
- Risk heatmap
- Ownership matrix
- Remediation tracker
- Vendor assessment register
Read also: Encryption Guide for DPDP Compliance
Days 31–60: Build Operational Controls
The second phase focuses on creating repeatable compliance processes.
Priority Activities
- Build rights request workflows
- Create processing records
- Implement retention schedules
- Update privacy notices
- Conduct employee training
Deliverables
- Rights management workflow
- Data inventory dashboard
- Updated policies
- Governance reporting framework
Days 61–90: Automate, Monitor, and Scale
The final phase transforms manual compliance into a sustainable operating model.
Priority Activities
- Automate compliance workflows
- Implement dashboards
- Schedule audits
- Monitor controls
- Track KPIs
Deliverables
- Executive compliance dashboard
- Automated evidence repository
- Board reporting pack
- Continuous monitoring program
Related Resource: DPDP Compliance Automation
How to Prioritize DPDP Compliance Gaps
Not every issue should receive equal attention.
High Priority
- Consent failures
- Rights request failures
- Sensitive data exposure
- Breach response weaknesses
Medium Priority
- Policy updates
- Reporting improvements
- Vendor documentation gaps
Low Priority
- Cosmetic workflow improvements
- Minor administrative issues
This approach ensures resources focus on the highest regulatory risks first.
Weekly KPIs to Track During DPDP Implementation
Organizations should measure execution progress using objective metrics.
Recommended KPIs include:
- Percentage of systems mapped
- Percentage of vendors reviewed
- Rights request readiness score
- Open critical remediation items
- Policy approval completion rate
- Evidence collection status
- Executive risk score trend
Why Unified GRC Platforms Accelerate DPDP Compliance?
Many organizations begin with spreadsheets, emails, and manual trackers.
While these tools may support assessments, they rarely support long-term compliance operations.
Modern GRC platforms help organizations:
- Centralize compliance activities
- Automate workflows
- Manage vendor risks
- Track remediation activities
- Maintain audit evidence
- Monitor compliance continuously
Conclusion
A DPDP compliance roadmap helps organizations move from assessments and compliance planning to measurable execution. By focusing on governance, Personal Data Discovery, Data Inventory & ROPA, Consent Management, Data Principal Rights Management, Vendor Risk Management Under DPDP, security controls, and audit readiness, organizations can build a structured and sustainable compliance program.
The 90-day implementation model provides a practical approach to prioritizing high-risk gaps, establishing operational controls, and automating ongoing compliance activities. Rather than treating DPDP as a one-time project, organizations should adopt a continuous governance model that combines privacy, security, risk management, and accountability.
Organizations that start early, assign clear ownership, and leverage modern GRC Platforms and Compliance Automation solutions will be better positioned to reduce compliance risks, improve audit readiness, and demonstrate accountability under the Digital Personal Data Protection Act.
FAQs
A DPDP compliance roadmap is a structured implementation plan that helps organizations manage personal data, implement privacy controls, handle Data Principal rights, manage vendor risks, and maintain audit readiness.
Related Posts