
Data Discovery
Discover and track personal data across your systems
Products • Data Discovery
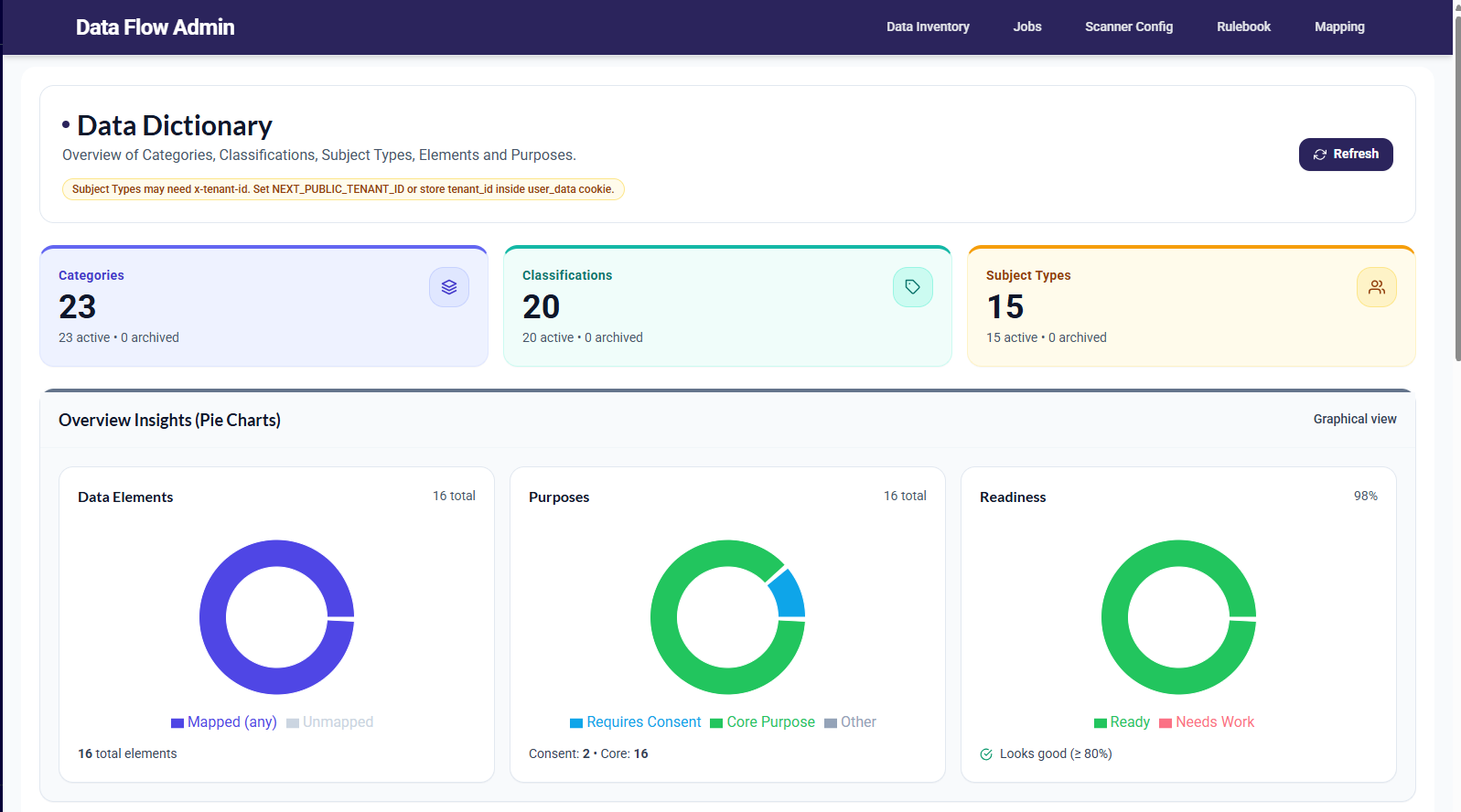
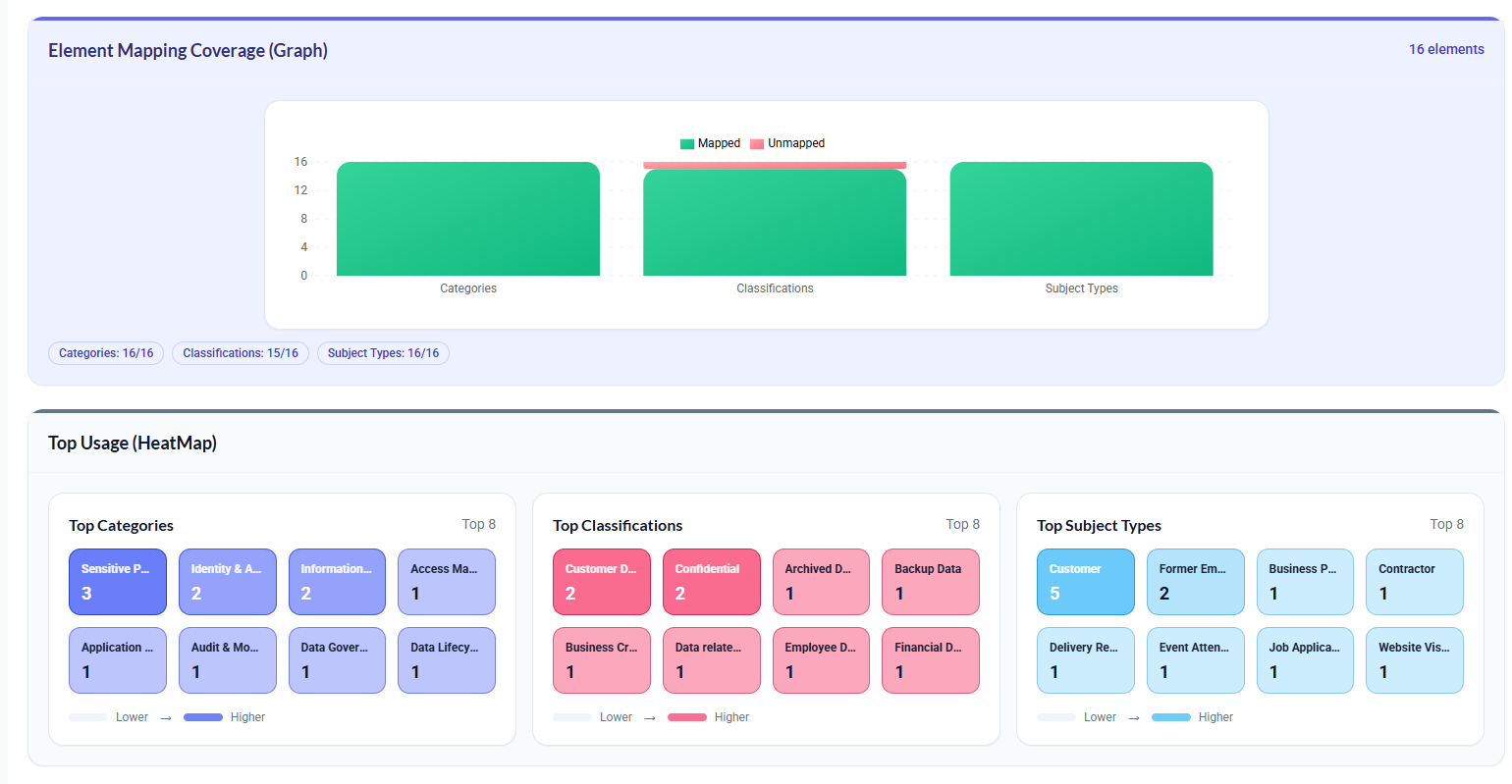
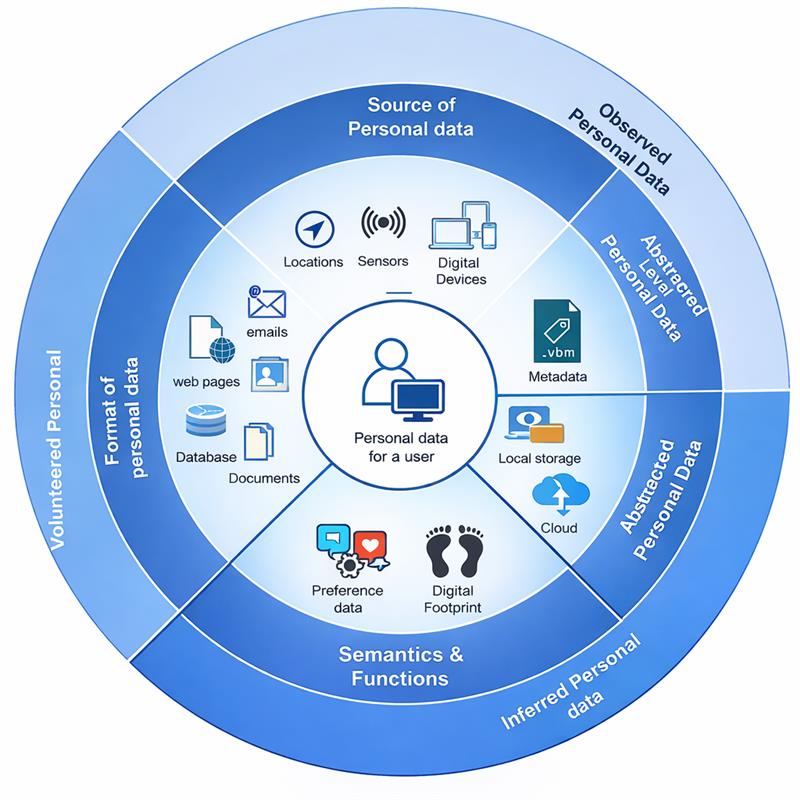
Find, understand, and govern personal data across your organization.
Automatically discover personal data across systems, reduce blind spots, and turn visibility into action with centralized governance.
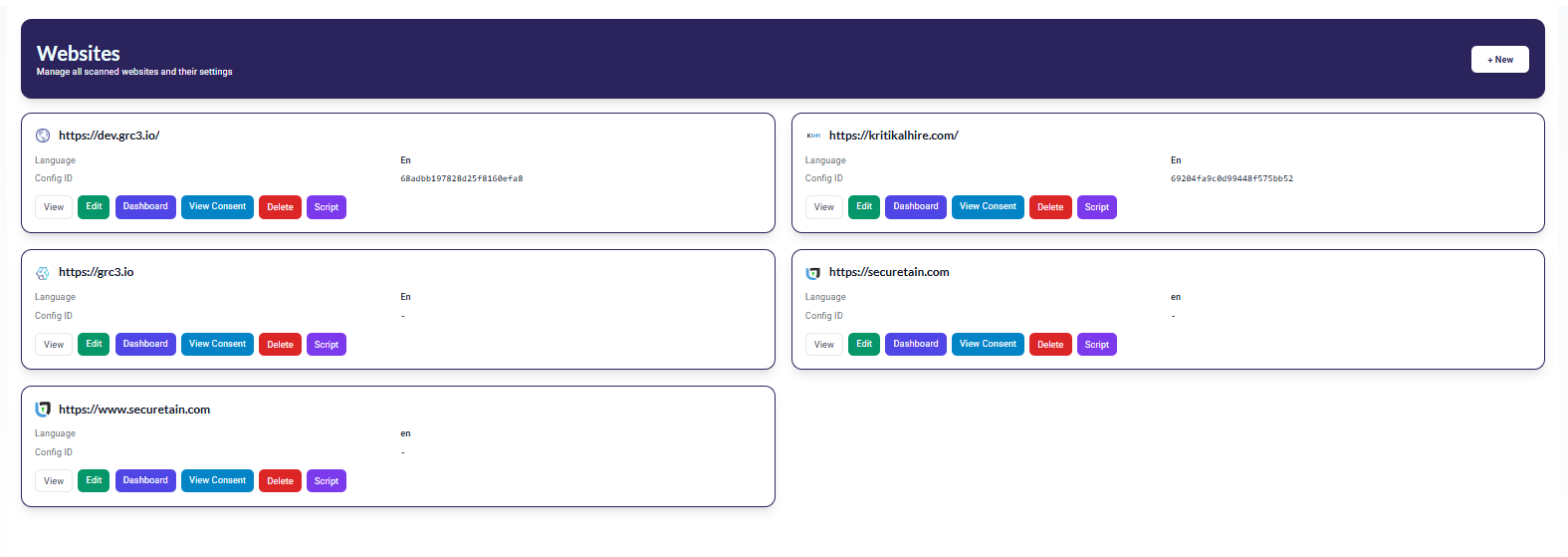
Scan across cloud, SaaS, on-prem, messaging apps, data lakes, AI pipelines, and hybrid environments.
Uncover shadow data, dark data, and unknown assets across your enterprise.
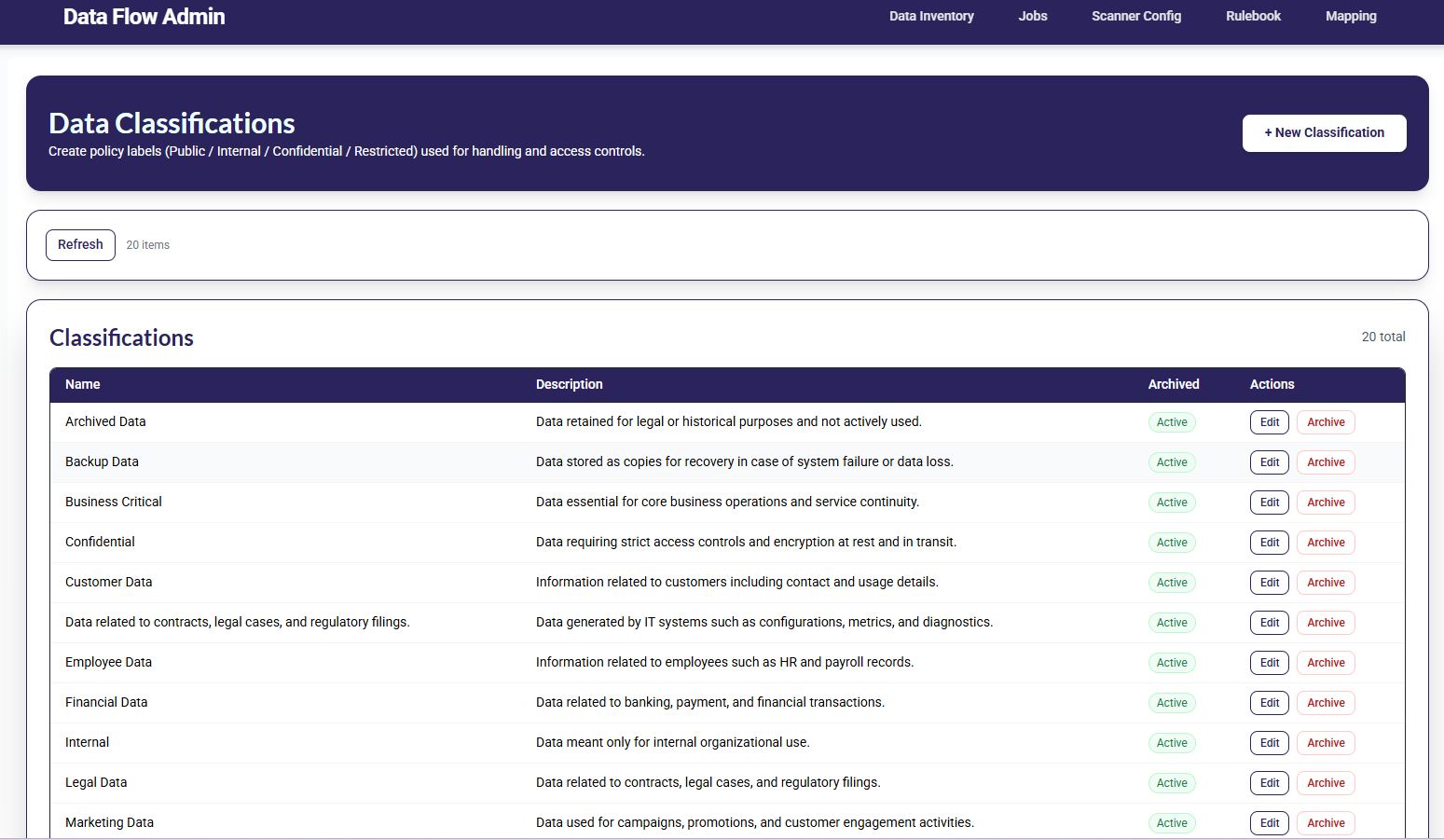
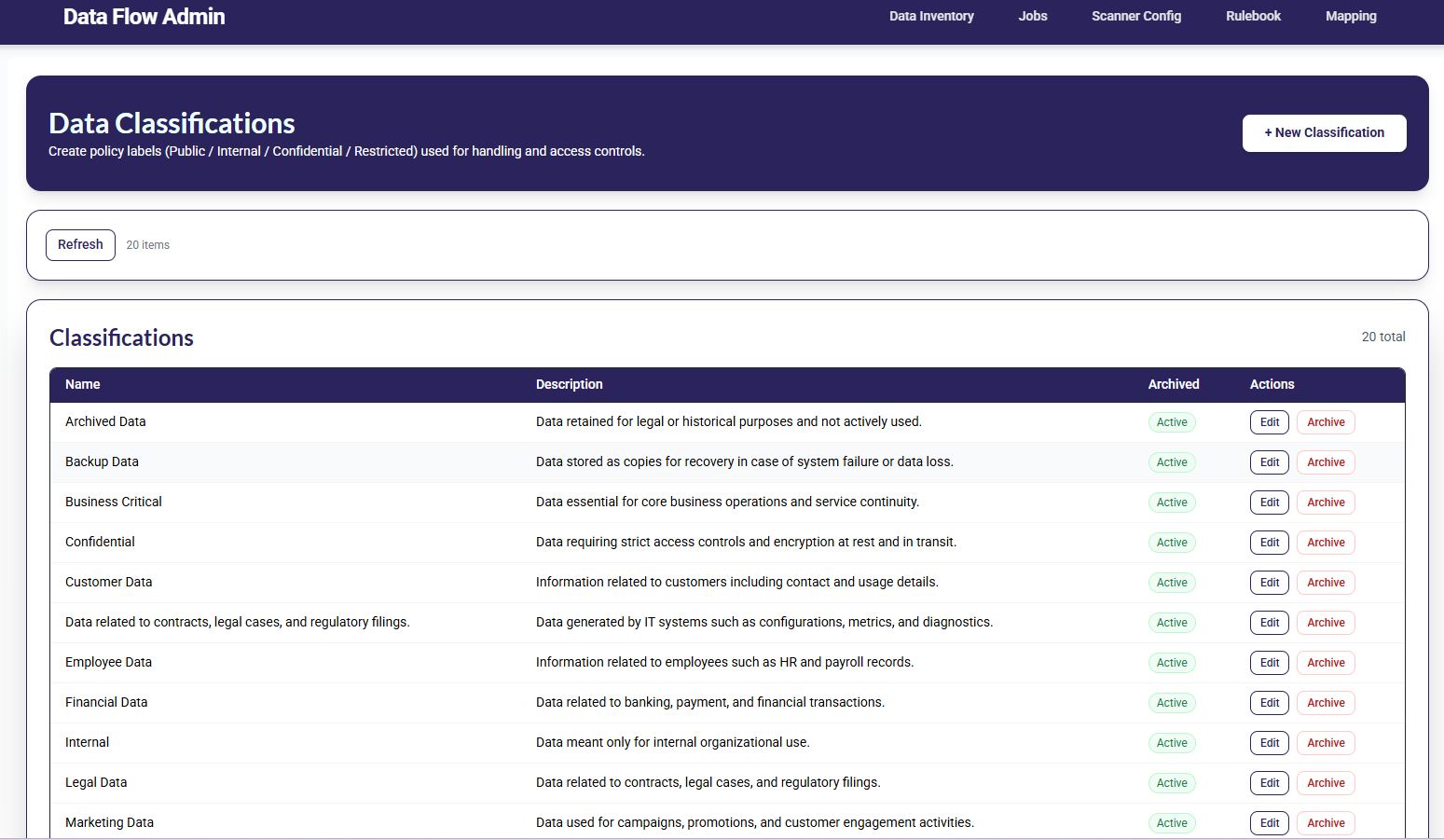
Refine classification models to fit your environment and data types.
Use ML, NLP, and pattern recognition to identify PII, PHI, credentials, secrets, and sensitive data clusters.
Tune classifiers to your environment for higher accuracy and fewer false positives.
Go beyond discovery with quarantine, remediation, deletion, minimization, and automated actions.
Automate remediation to quarantine, redact, delete, minimize, or label sensitive data.
Apply policy-driven controls for privacy, security, retention, and residency across your data landscape.
Identify data feeding copilots, chatbots, and AI models so responsible AI teams have full visibility.
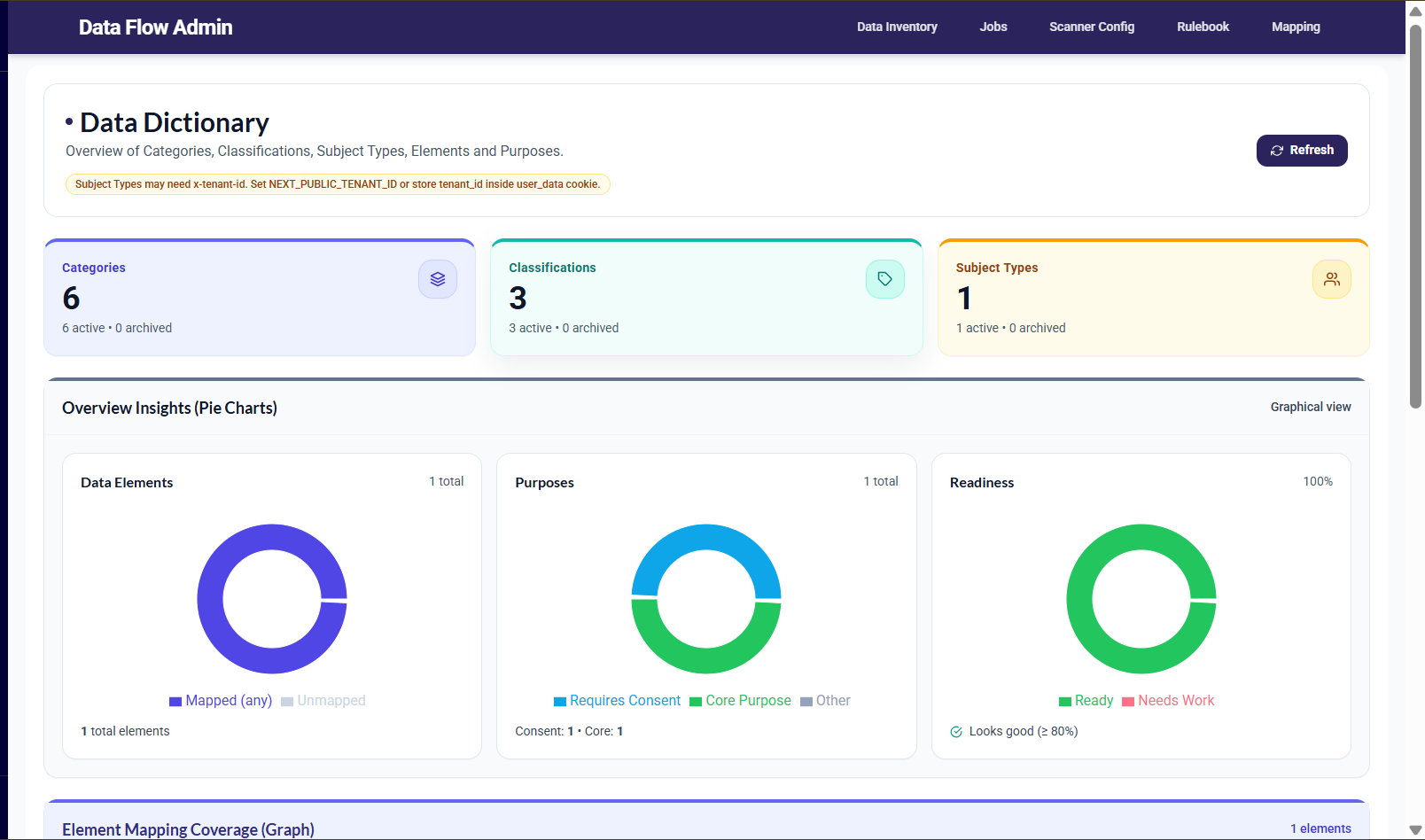
GRC3 combines classifier tuning, intuitive data exploration, and easy scanning to turn data discovery into a strategic advantage.
Data Explorer lets you visualize, filter, and drill into discovered data so teams can act without heavy manual effort.
Visualize where personal data flows, how it is processed, and who can access it with centralized governance and audit-ready visibility.
Visualize data movement across cloud, SaaS, on-prem, and hybrid environments.
Track processing steps, storage points, and where data is shared or transferred.
Identify access points, owners, and processors to reduce blind spots across workflows.
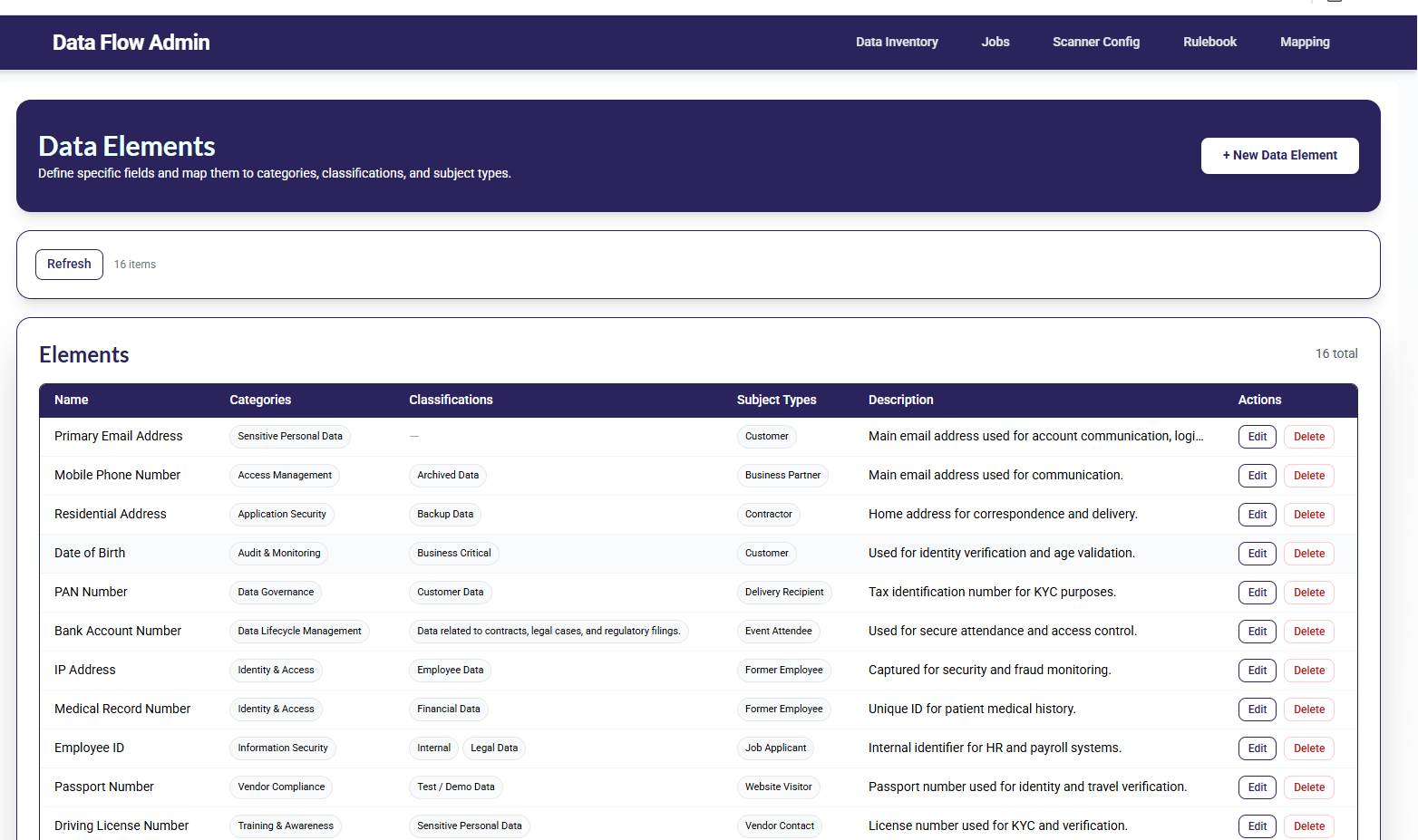
Document processing activities and how personal data is used across features, teams, and systems.
Identify who can access data, where it is stored, and where it is shared with vendors or third parties.
Reduce risk by spotting unnecessary data movement, over-sharing, and high-risk transfers early.
Assign ownership for flows, systems, and processors to drive accountability across teams.
Apply governance controls for privacy, security, residency, and retention based on mapped flows.
Validate data movement and sharing before new features go live so teams can ship faster.
Data Mapping brings clarity to your processing landscape so privacy, security, and product teams can align on how personal data moves.
Visualize flows, identify sharing points, and keep documentation audit-ready without heavy manual effort or scattered spreadsheets.
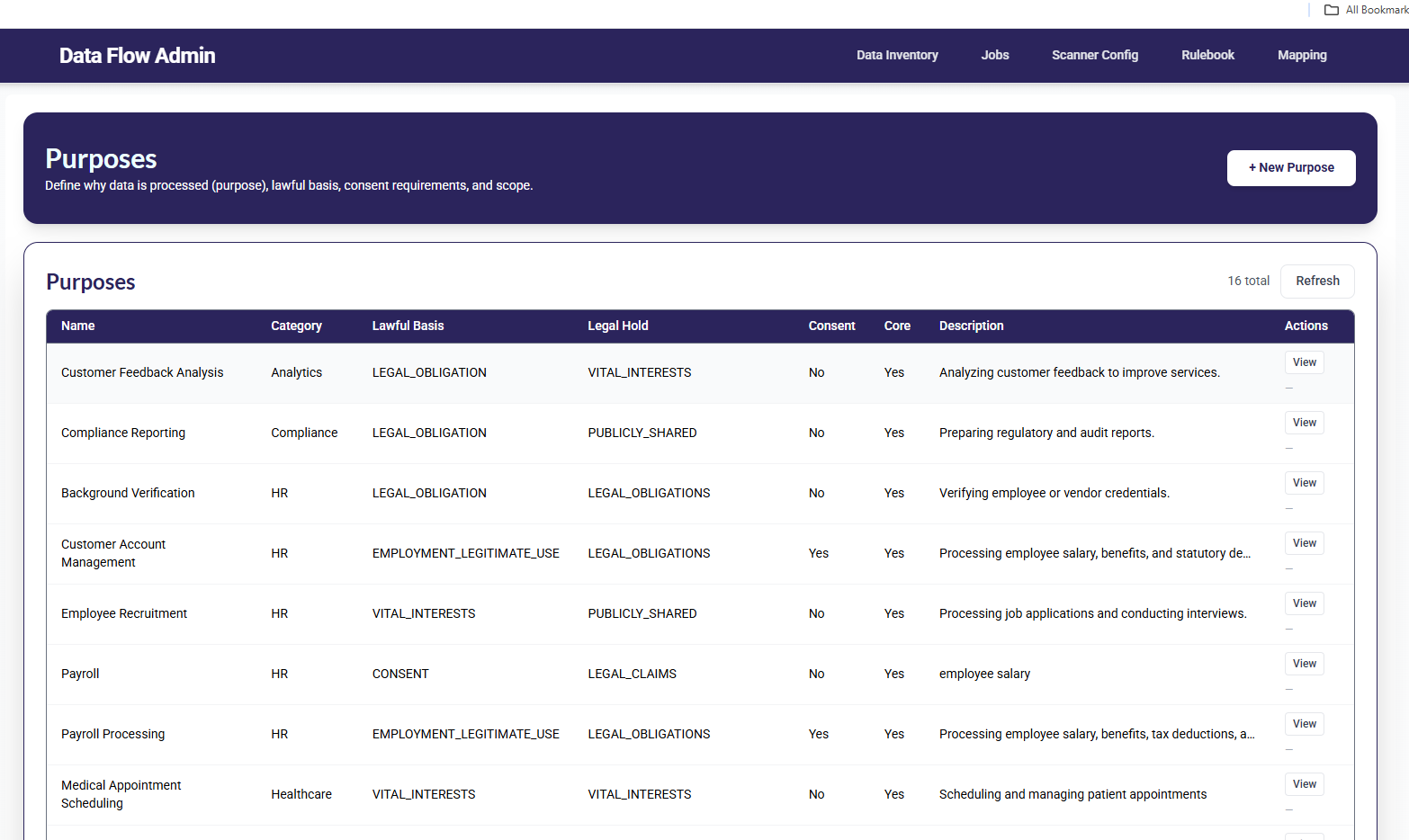
Set retention policies, track data lifecycles, and automate deletion across systems with audit-ready visibility that reduces risk and improves governance.

Set retention periods by data category, purpose, and business need across your organization.
Align retention to operational requirements while ensuring data is not kept longer than necessary.
Assign owners and enforce policies consistently across teams and systems.
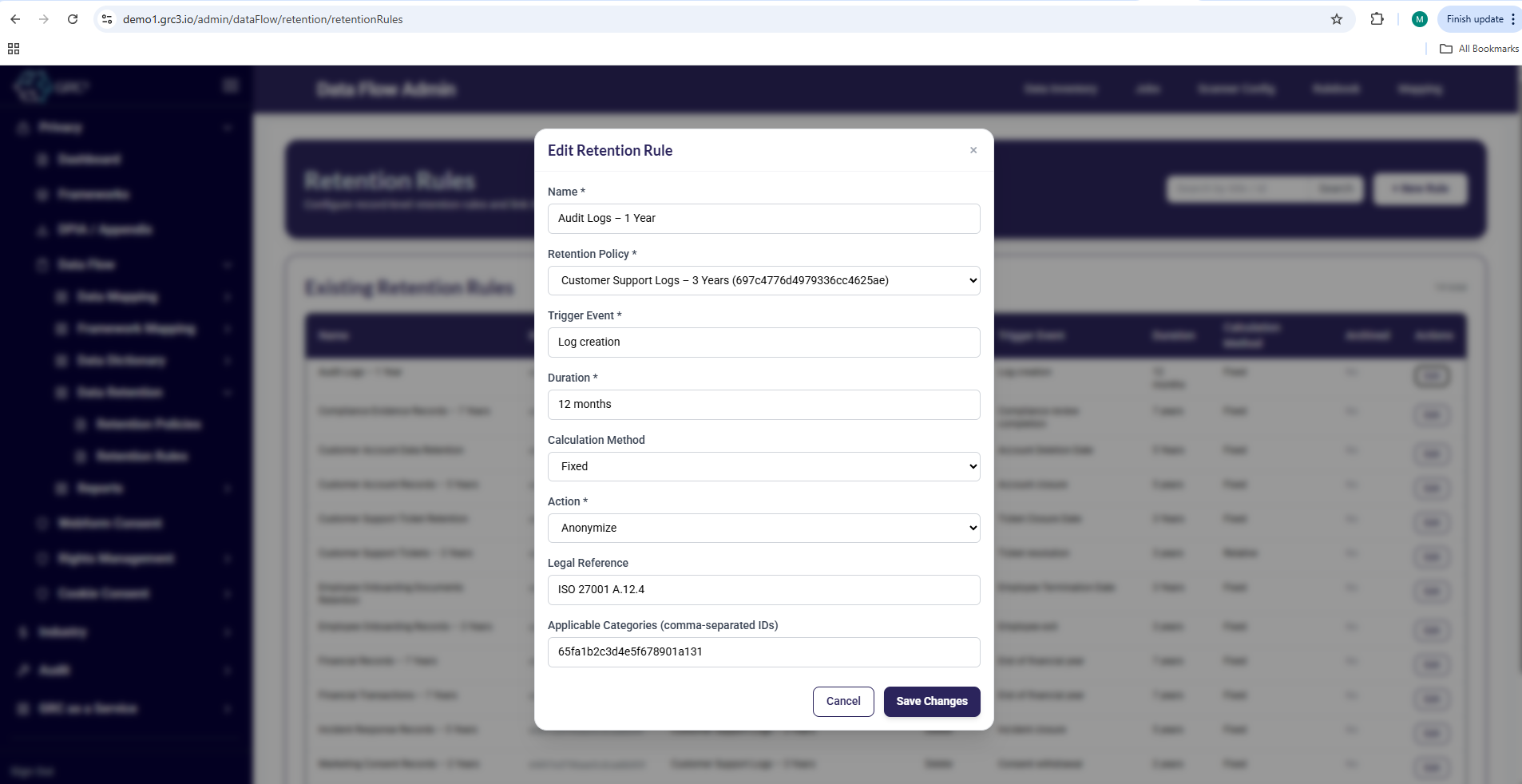
Trigger policy-based actions when data reaches end of life and delete, archive, or anonymize automatically.
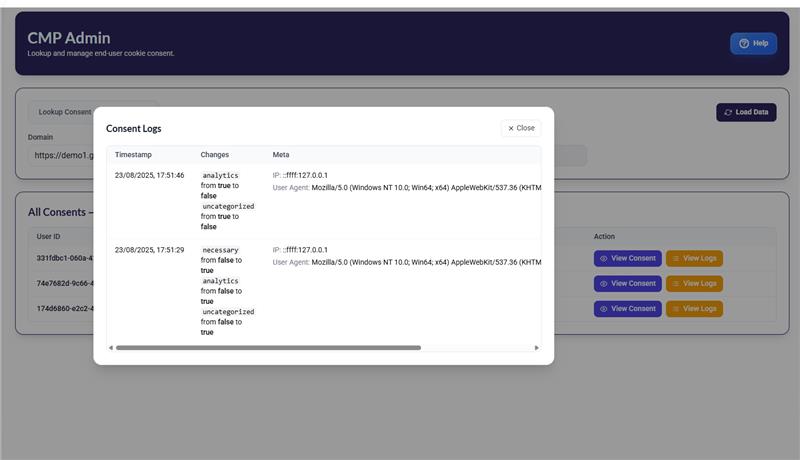
Collect deletion confirmations and maintain evidence trails to support audits and internal reviews.
Reduce manual coordination by automating workflows across internal systems and third-party tools.
Minimize stored personal data to reduce breach impact and lower long-term compliance exposure.
Enforce retention consistently across business apps, databases, storage, and third-party processors.
Track execution and keep audit-ready proof of policy enforcement and deletion outcomes.
Data Retention turns policy into practice by helping teams enforce timelines, reduce stored data, and maintain proof of compliant deletion.
Track what should be retained, what should be deleted, and when with workflow visibility that stays audit-ready without heavy manual effort.
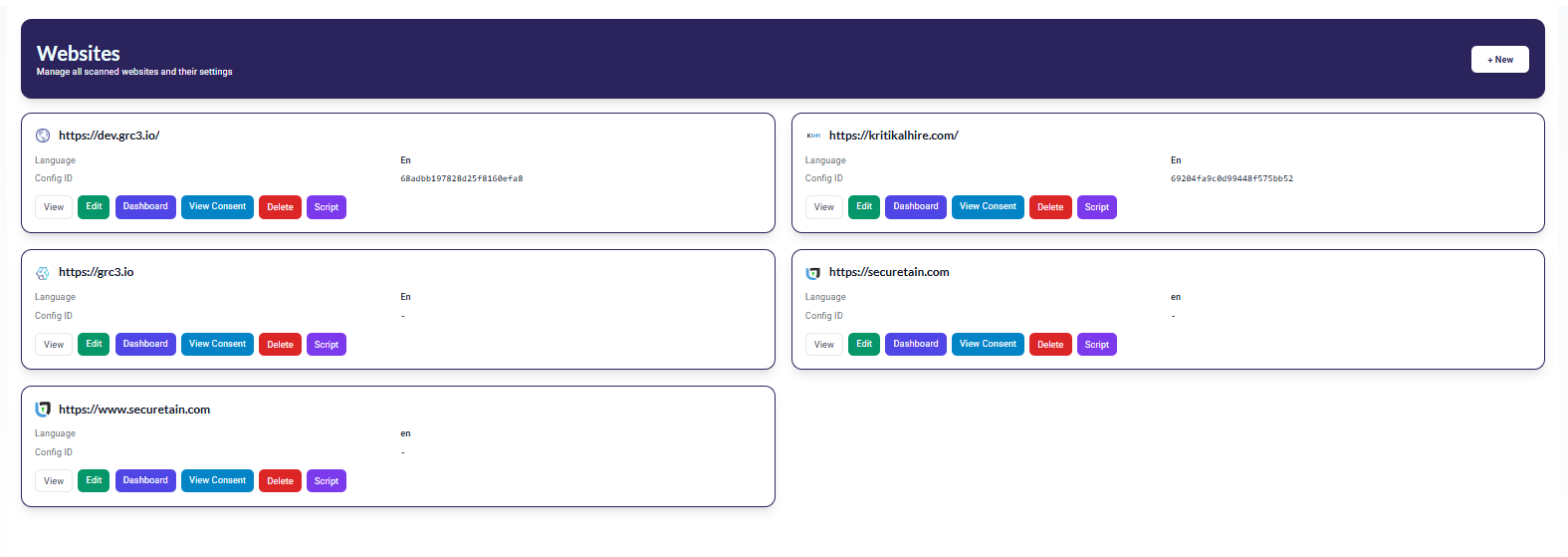
Navigate through modules to discover, classify, and map personal data across your systems.

Discover and track personal data across your systems

Map personal data flows for DPDP compliance

Ensure data is retained and deleted as per DPDP requirements

Seamlessly integrate with cloud platforms, emails, and databases to detect and classify personal data.
Extract names, tax numbers, email addresses, and sensitive data from unstructured sources.

Instantly locate relevant personal data for compliance, audits, and security assessments.

Retrieve, protect, or delete personal data to support compliance and security measures.
Where traditional validation meets AI-powered data discovery - for outcomes you can trust.
Tip: click a module to see the overview, benefits, and preview.
PRODUCT OVERVIEW
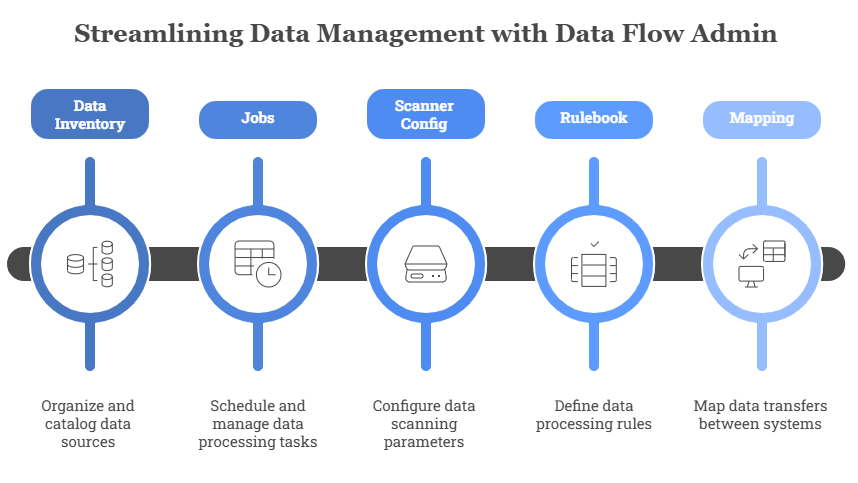
Map end-to-end data movement across apps, teams, and vendors to reduce blind spots, strengthen governance, and support DPDP-aligned accountability.
Search, locate, and act on personal data from emails, documents, cloud drives, databases, and endpoints. Built for compliance and security teams that must move from discovery to results fast.
Scan emails, documents, PDFs, cloud storage, and endpoints to keep tabs on every piece of personal data.
Spot names, IDs, tax numbers, emails, and phone numbers with precision across structured and unstructured data.
Get instant answers and indexed previews so you can act on requests, audits, and investigations without delay.
Handle massive data volumes with confidence—search runs smoothly even across large estates and compliance fleets.
Highlights
PDS enables fast, precise identification of personal data across unstructured sources, giving organizations full visibility and control while supporting regulatory compliance and security best practices.

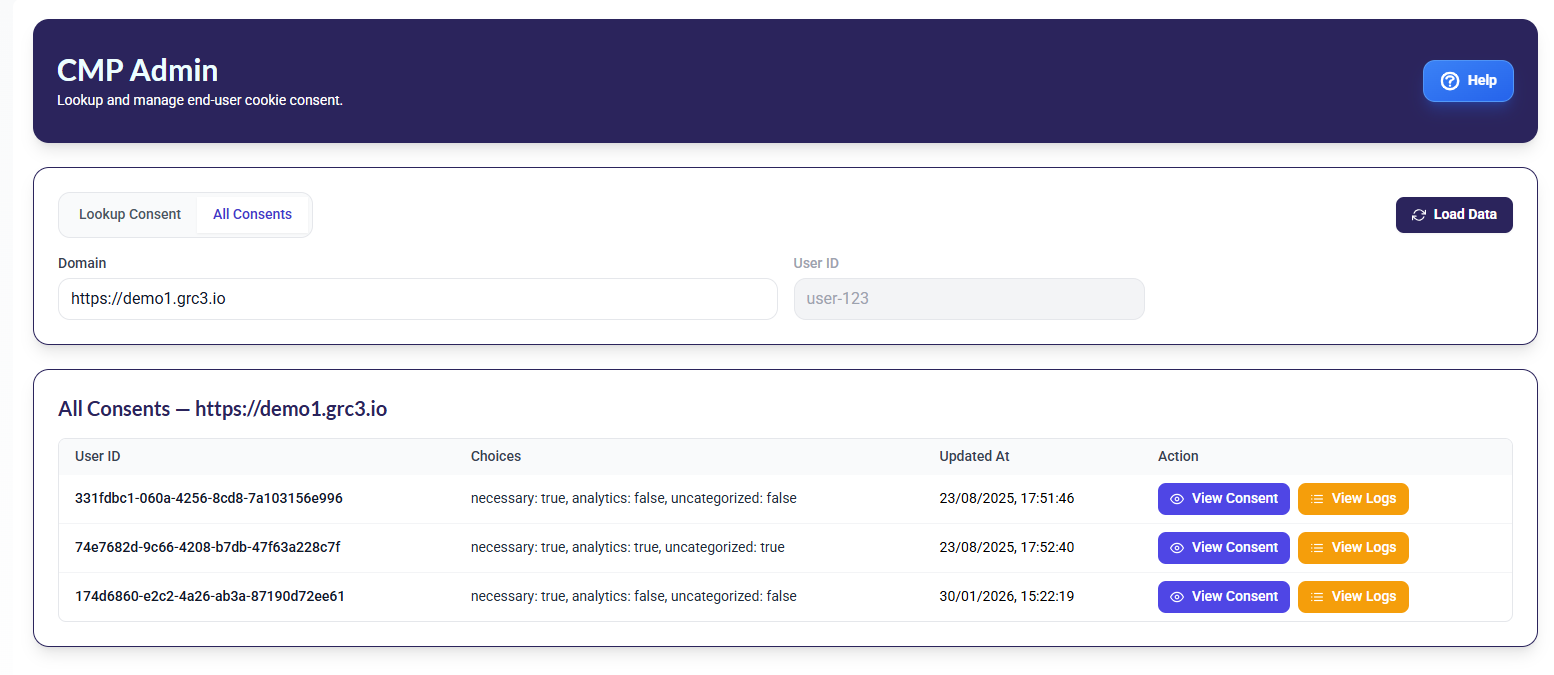
Streamline responses to Data Subject Requests by quickly retrieving all relevant documents associated with an individual, aiding in adherence to global privacy regulations.

During a breach, run large-scale searches to determine where exposed personal data exists. Gain full visibility into unstructured data sources to proactively manage risk and safeguard sensitive information.

Identify redundant or outdated personal data to meet retention and deletion policies. Ensure personal data is fully removed by searching across all sources for residual traces.

Benefits
Efficiently process and scan millions of documents, reducing the time and resources required for manual searches, ensuring faster, more accurate personal data search.
Search for sensitive and exposed data that could pose security threats, and take action before breaches occur.
Reduce the time needed to process DSARs by instantly locating and retrieving all personal data related to an individual.
Take control of your data and simplify compliance with Personal Data Search (PDS). Get a personalized walkthrough and see how PDS can transform your discovery process.
Explore the insights and trends shaping our industry.

Understand when India's DPDP Act mandates DPIAs and how to stay compliant.

Break down DPDP-aligned risk scoring inside your DPIA with practical guidance.